What Is Remote Browser Isolation (RBI)? How It Works in Plain English
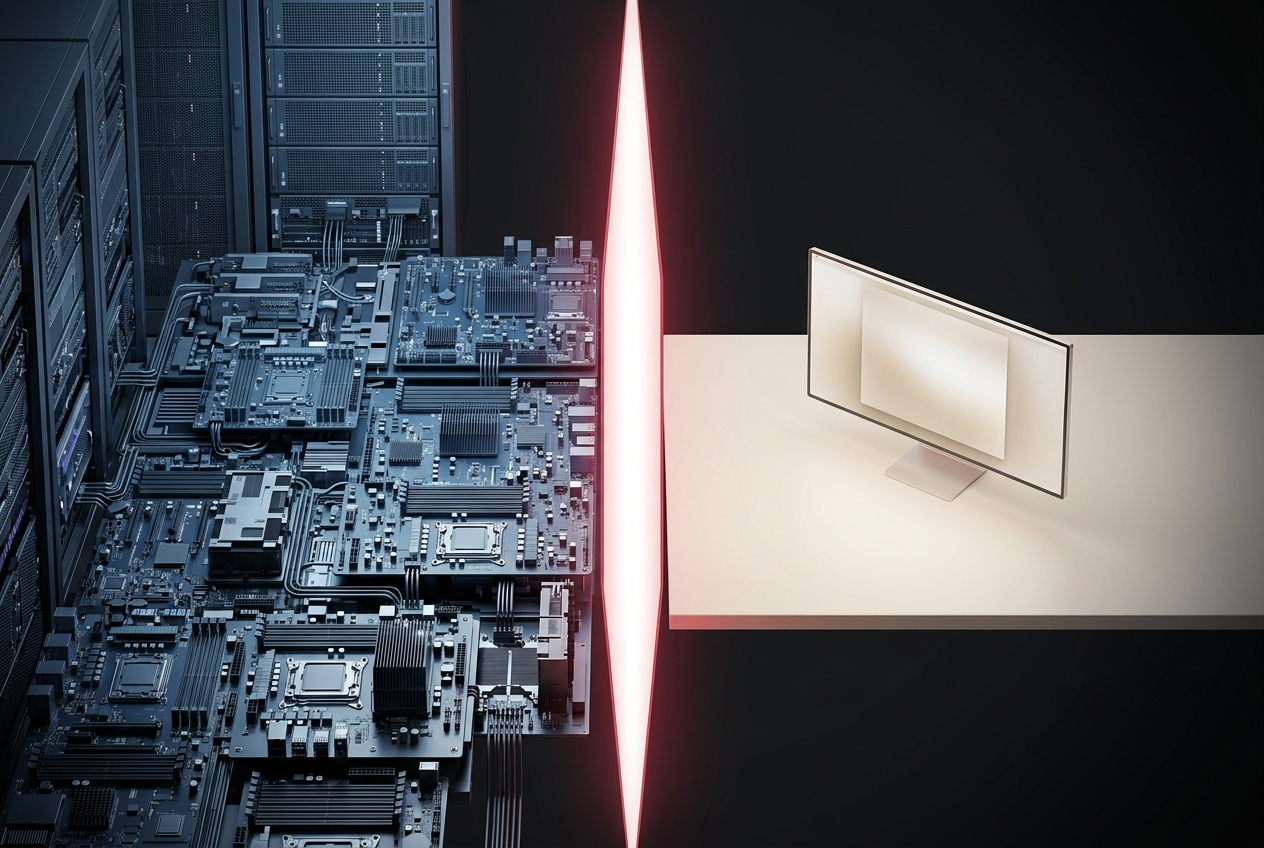
Remote browser isolation (RBI) moves web browsing to a remote server or edge node. Your device receives safe rendered output while threats execute in a disposable container. This guide explains three RBI architectures and the enterprise market in 2026.
Your security team deployed firewalls, endpoint detection, email filtering, and a VPN. The stack looks solid on paper. Then an employee clicks a link to what appears to be a routine invoice PDF on a supplier's website. The site was compromised two days ago. Malicious JavaScript executes in the browser, captures the employee's session cookies for three SaaS applications, and exfiltrates them before the page even finishes loading. None of the tools in the stack saw it, because the attack happened inside the browser.
This is the gap that Remote Browser Isolation (RBI) was built to close. Instead of trusting the local browser to safely handle whatever the web delivers, RBI moves that execution to a remote environment where threats are contained and destroyed.
Remote Browser Isolation in One Paragraph
Remote Browser Isolation (RBI)is a cybersecurity technology that executes web content on a remote server or edge node instead of on the user's local device. When a user visits a website, the page loads and renders in an isolated remote environment. The user's browser receives a safe visual representation (a pixel stream, a draw-command stream, or a sanitized DOM reconstruction). Malicious code, exploits, and tracking scripts execute in the remote environment and never reach the endpoint. When the session ends, the remote environment is destroyed.
How RBI Works, Step by Step
The RBI workflow follows four stages. Each stage applies regardless of the specific architectural approach.
Step 1: The User Requests a Web Page
The user navigates to a URL in their browser. Instead of the browser fetching the page directly, the RBI layer intercepts the request. Depending on policy configuration, the request is either routed to the remote isolation environment (for all traffic or for specific categories like uncategorized sites, newly registered domains, or known-risky URLs) or passed through to the local browser for trusted destinations.
Step 2: The Page Loads in a Remote Environment
The web page loads and renders inside an isolated container or virtual machine on remote infrastructure. All JavaScript, WebAssembly, plugins, and embedded content execute there. If the page contains malicious code, an exploit, or a phishing kit, it executes in the remote environment, completely separated from the user's device.
Step 3: Safe Output Is Sent to the User
The RBI system sends a safe representation of the rendered page back to the user's browser. The user sees and interacts with the page normally (scrolling, clicking, typing). The RBI layer translates user interactions into actions in the remote environment in real time.
Step 4: The Session Is Destroyed
When the user closes the tab or the session times out, the remote environment is destroyed. Cookies, cache, session tokens, browser state, and any malware that executed inside the container are eliminated. The next session starts from a completely clean state.
For the technical primer on this architecture, Legba publishes a lite paper on browser isolation technology.
Three Architectures of RBI
Not all RBI implementations work the same way. The differences in how safe output is delivered to the user have significant implications for performance, bandwidth, and user experience.
1. Pixel Pushing (Full Visual Stream)
The remote browser renders the page into an image or video stream and sends it to the user's browser frame by frame. This is conceptually similar to a remote desktop session. It provides the strongest isolation (no code whatsoever reaches the local browser) but consumes the most bandwidth and can feel sluggish for interactive applications. Every scroll, every hover state, and every animation requires a round trip.
2. DOM Reconstruction (Sanitized HTML)
The remote browser processes the page, strips all potentially dangerous code (JavaScript, iframes, embedded objects), and sends a sanitized version of the page's HTML, CSS, and safe assets to the local browser for rendering. This approach uses less bandwidth than pixel pushing and feels more responsive because the local browser handles rendering. However, some complex web applications may not render correctly after sanitization.
3. Browser-Native Edge Isolation
Web content executes at the network edge, close to the user, using distributed infrastructure. Instead of routing traffic to a centralized cloud data center, the isolation happens at the nearest edge node. This minimizes latency while maintaining strong isolation. This architecture is typically delivered through a browser extension rather than a network appliance, making deployment significantly simpler. This is the approach Legba uses.
| Dimension | Pixel Pushing | DOM Reconstruction | Edge Isolation |
|---|---|---|---|
| Output to user | Image/video stream | Sanitized HTML/CSS | Safe rendered content |
| Bandwidth usage | High | Low to moderate | Moderate |
| Latency | High (every interaction round-trips) | Low (local rendering) | Low (geographically close) |
| Web app compatibility | Full (remote browser is complete) | Partial (sanitization may break complex apps) | High |
| Isolation strength | Strongest (no code sent) | Strong (sanitized code) | Strong (edge-based execution) |
What RBI Stops That Other Tools Cannot
RBI addresses the specific threat category that executes inside the browser session. These are threats that firewalls, VPNs, and endpoint detection tools are architecturally unable to prevent.
- Phishing and credential harvesting. Fake login pages execute in the remote environment, isolated from real credential stores.
- Zero-day browser exploits. Exploits trigger in the remote container and are destroyed with it. The local browser is never exposed.
- Drive-by downloads.Malicious files are downloaded into the disposable environment, not onto the user's file system.
- Malicious JavaScript and WebAssembly. Code executes remotely. The local device never processes it.
- Session hijacking. Session tokens exist only in the remote environment and are destroyed when the session ends.
For specific browser-based threat patterns, see the browser threat playbook library.
RBI vs Browser Isolation: Is There a Difference?
The terms "browser isolation" and "remote browser isolation" are often used interchangeably, but there is a technical distinction.
Browser isolation is the broad category. It includes any technology that separates web content execution from the local device. This encompasses local sandboxing, cloud-based RBI, and browser-native edge isolation.
Remote browser isolationis a subset. It specifically refers to approaches where web content executes on infrastructure that is remote from the user's device: a cloud server, a data center, or an edge node.
In practice, most modern browser isolation products use remote execution (either cloud or edge), so the terms overlap heavily. For the broader overview, see What Is Browser Isolation? The Complete 2026 Guide.
The Enterprise RBI Market in 2026
RBI is no longer an experimental technology. The market was estimated at $1.04 billion in 2025 and is projected to reach $3.25 billion by 2029, growing at a compound annual rate above 30% according to industry analyst estimates.
Several enterprise trends are accelerating adoption:
- Zero trust mandates. NIST SP 800-207 and similar frameworks require security controls at every layer, including the application layer. RBI provides zero trust at the browser level.
- BYOD expansion. With unmanaged devices accessing corporate applications, RBI protects the session without requiring endpoint management software.
- Browser as the work environment. An estimated 85% of knowledge work now happens in browser tabs. The browser is no longer just an application. It is the primary interface for enterprise work.
- Compliance requirements. Regulations in financial services, healthcare, and government increasingly require isolation of sensitive data from endpoints.
For context on why browser-level attacks are particularly devastating for smaller organizations, see Why 60% of Small Businesses Shut Down After a Cyberattack.
Common Objections to RBI (And the Reality)
- "RBI is too slow."Early RBI implementations using pixel-pushing architecture did add noticeable latency. Modern edge-based solutions process isolation close to the user, making the latency negligible for most use cases. Cloudflare's draw-command approach and Legba's edge-based model both prioritize performance.
- "Users will resist the experience change." Browser-native approaches (delivered as Chrome extensions) feel like normal browsing. Users do not interact with a remote desktop or a visibly different browser. Adoption friction is significantly lower than with earlier RBI generations.
- "It is too expensive for our budget."Enterprise RBI pricing has historically been opaque. Consumer options now start at $10 per month (Legba) with no enterprise sales cycle required. The cost of a single breach ($4.88 million average in 2024, according to IBM's Cost of a Data Breach Report) makes isolation economics straightforward.
- "Deployment is too complex." Network-appliance-based RBI required infrastructure changes. Extension-based deployment (Legba, LayerX) requires installing a Chrome extension. No network routing changes. No proxy configurations. No browser replacement.
Where Legba Fits
Legba uses the browser-native edge isolation architecture. Web content executes at the network edge, close to the user, with minimal latency. It is delivered as a Chrome extension with no infrastructure changes required.
- $10 per month for individual use
- MSP platform for managing isolation across client organizations
- Ephemeral sessions destroyed on tab close
- Ghost Mode for visible isolation state
- 15+ country exit points for geographic routing
For the full architectural deep dive, see How Legba's Browser-Native Isolation Actually Protects You. For the product comparison, see 5 Best Browser Isolation Extensions for Chrome in 2026.
Continue the RBI Deep Dive
The browser isolation pillar guide, the technical architecture, and the Chrome extension comparison.
What Is Browser Isolation? The Complete 2026 Guide
Browser isolation moves web content execution away from your device so that malicious code, phishing kits, and exploits never touch your endpoint. This is the complete 2026 guide.
How Legba's Browser-Native Isolation Actually Protects You: A Technical Deep Dive
A technical deep dive into how Legba's browser-native isolation actually works, from edge-based execution to ephemeral containers to threat-by-threat protection.
5 Best Browser Isolation Extensions for Chrome in 2026
The browser isolation market is growing fast. Here are the five Chrome-compatible options worth evaluating in 2026, with honest pros, cons, and the use case each one fits best.
See Edge-Based RBI in Action
Legba brings remote browser isolation to Chrome without the infrastructure complexity. $10 per month. No network changes. No separate browser.